-
Latest Version
-
Operating System
Mac OS X
-
User Rating
Click to vote -
Author / Product
-
Filename
jdk-8u121-macosx-x64.dmg
-
MD5 Checksum
053951fc1fa47569ff42a99d147cfa07
Sometimes latest versions of the software can cause issues when installed on older devices or devices running an older version of the operating system. Software makers usually fix these issues but it can take them some time. What you can do in the meantime is to download and install an older version of Java JDK 8 Update 121.
For those interested in downloading the most recent release of Java Development Kit for Mac or reading our review, simply click here.
All old versions distributed on our website are completely virus-free and available for download at no cost.
We would love to hear from you
If you have any questions or ideas that you want to share with us - head over to our Contact page and let us know. We value your feedback!
-
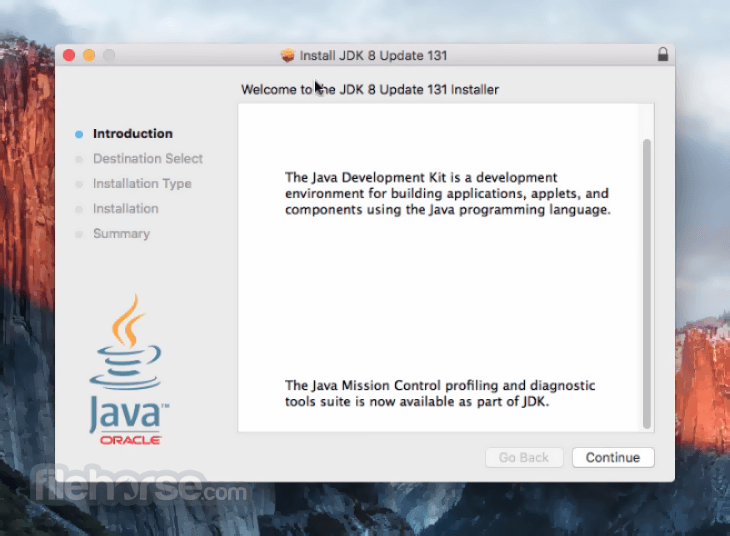
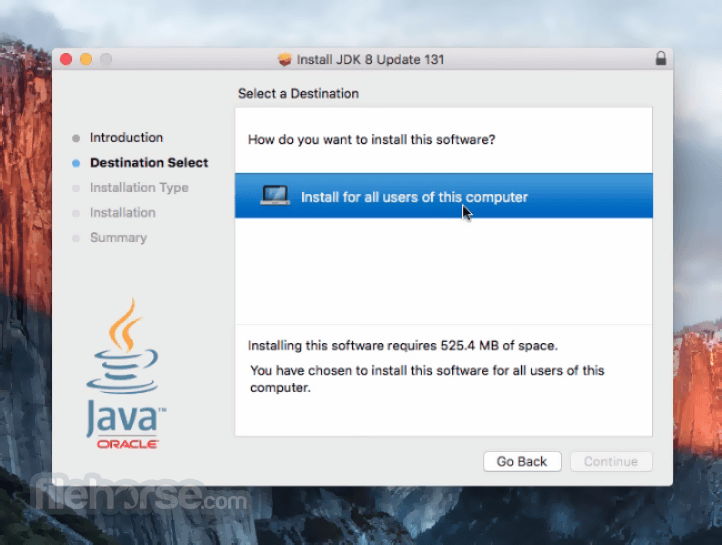
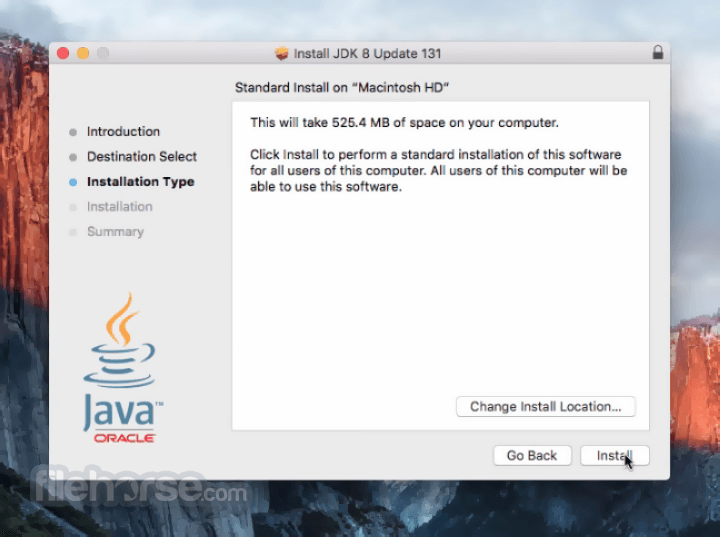
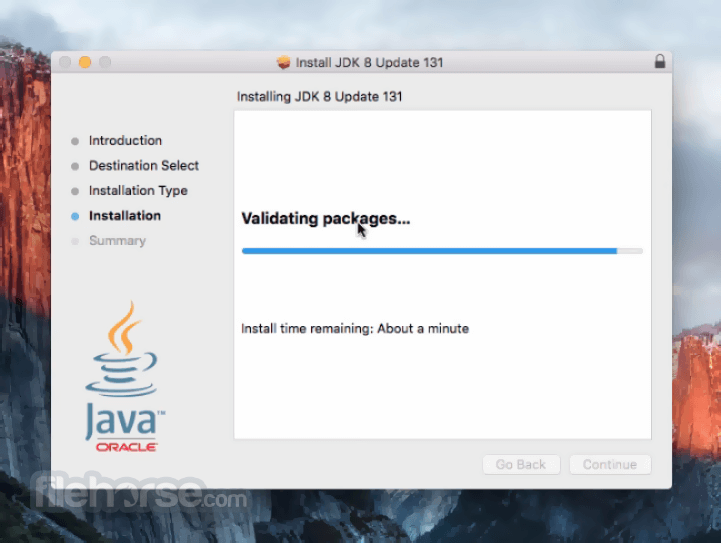
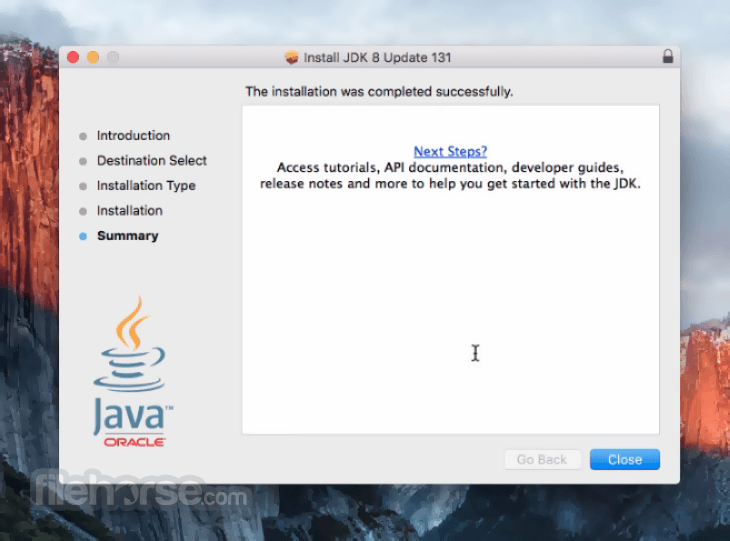
Java JDK 8 Update 121 Screenshots
The images below have been resized. Click on them to view the screenshots in full size.
What's new in this version:
New features:
RMI Better constraint checking:
- RMI Registry and Distributed Garbage Collection use the mechanisms of JEP 290 Serialization Filtering to improve service robustness
- RMI Registry and DGC implement built-in white-list filters for the typical classes expected to be used with each service
- Additional filter patterns can be configured using either a system property or a security property. The "sun.rmi.registry.registryFilter" and "sun.rmi.transport.dgcFilter" property pattern syntax is described in JEP 290 and in /lib/security/java.security
- JDK-8156802 (not public)
Add mechanism to allow non-default root CAs to not be subject to algorithm restrictions:
- New certpath constraint: jdkCA*
- In the java.security file, an additional constraint named "jdkCA" is added to the jdk.certpath.disabledAlgorithms property. This constraint prohibits the specified algorithm only if the algorithm is used in a certificate chain that terminates at a marked trust anchor in the lib/security/cacerts keystore. If the jdkCA constraint is not set, then all chains using the specified algorithm are restricted. jdkCA may only be used once in a DisabledAlgorithm expression.
- Example: To apply this constraint to SHA-1 certificates, include the following: SHA1 jdkC
Changes:
- The secure validation mode of the XML Signature implementation has been enhanced to restrict RSA and DSA keys less than 1024 bits by default as they are no longer secure enough for digital signatures. Additionally, a new security property named jdk.xml.dsig.SecureValidationPolicy has been added to the java.security file and can be used to control the different restrictions enforced when the secure validation mode is enabled.
- The secure validation mode is enabled either by setting the xml signature property org.jcp.xml.dsig.secureValidation to true with the javax.xml.crypto.XMLCryptoContext.setProperty method, or by running the code with a SecurityManager.
- If an XML Signature is generated or validated with a weak RSA or DSA key, an XMLSignatureException will be thrown with the message, "RSA keys less than 1024 bits are forbidden when secure validation is enabled" or "DSA keys less than 1024 bits are forbidden when secure validation is enabled."
Restrict certificates with DSA keys less than 1024 bits:
- DSA keys less than 1024 bits are not strong enough and should be restricted in certification path building and validation. Accordingly, DSA keys less than 1024 bits have been deactivated by default by adding "DSA keySize < 1024" to the "jdk.certpath.disabledAlgorithms" security property. Applications can update this restriction in the security property ("jdk.certpath.disabledAlgorithms") and permit smaller key sizes if really needed (for example, "DSA keySize < 768").
More checks added to DER encoding parsing code:
- More checks are added to the DER encoding parsing code to catch various encoding errors. In addition, signatures which contain constructed indefinite length encoding will now lead to IOException during parsing. Note that signatures generated using JDK default providers are not affected by this change.
Additional access restrictions for URLClassLoader.newInstance:
- Class loaders created by the java.net.URLClassLoader.newInstance methods can be used to load classes from a list of given URLs. If the calling code does not have access to one or more of the URLs and the URL artifacts that can be accessed do not contain the required class, then a ClassNotFoundException, or similar, will be thrown. Previously, a SecurityException would have been thrown when access to a URL was denied. If required to revert to the old behavior, this change can be disabled by setting the jdk.net.URLClassPath.disableRestrictedPermissions system property.
A new configurable property in logging.properties java.util.logging.FileHandler.maxLocks:
- A new "java.util.logging.FileHandler.maxLocks" configurable property is added to java.util.logging.FileHandler.
- This new logging property can be defined in the logging configuration file and makes it possible to configure the maximum number of concurrent log file locks a FileHandler can handle. The default value is 100.
- In a highly concurrent environment where multiple (more than 101) standalone client applications are using the JDK Logging API with FileHandler simultaneously, it may happen that the default limit of 100 is reached, resulting in a failure to acquire FileHandler file locks and causing an IO Exception to be thrown. In such a case, the new logging property can be used to increase the maximum number of locks before deploying the application.
- If not overridden, the default value of maxLocks (100) remains unchanged. See java.util.logging.LogManager and java.util.logging.FileHandler API documentation for more details.
Bug fixes:
Trackpad scrolling of text on OS X 10.12 Sierra is very fast:
- The MouseWheelEvent.getWheelRotation() method returned rounded native NSEvent deltaX/Y events on Mac OS X. The latest macOS Sierra 10.12 produces very small NSEvent deltaX/Y values so rounding and summing them leads to the huge value returned from the MouseWheelEvent.getWheelRotation(). The JDK-8166591 fix accumulates NSEvent deltaX/Y and the MouseWheelEvent.getWheelRotation() method returns non-zero values only when the accumulated value exceeds a threshold and zero value. This is compliant with the MouseWheelEvent.getWheelRotation() specification
- "Returns the number of "clicks" the mouse wheel was rotated, as an integer. A partial rotation may occur if the mouse supports a high-resolution wheel. In this case, the method returns zero until a full "click" has been accumulated."
- For the precise wheel rotation values, use the MouseWheelEvent.getPreciseWheelRotation() method instead.
- This release also contains fixes for security vulnerabilities described in the Oracle Java SE Critical Patch Update Advisory available at http://www.oracle.com/technetwork/security-advisory/cpujan2017-2881727.html.
Notes:
Improved protection for JNDI remote class loading:
- Remote class loading via JNDI object factories stored in naming and directory services is disabled by default. To enable remote class loading by the RMI Registry or COS Naming service provider, set the following system property to the string "true", as appropriate: com.sun.jndi.rmi.object.trustURLCodebase and com.sun.jndi.cosnaming.object.trustURLCodebase
jarsigner -verbose -verify should print the algorithms used to sign the jar:
- The jarsigner tool has been enhanced to show details of the algorithms and keys used to generate a signed JAR file and will also provide an indication if any of them are considered weak.
- Specifically, when "jarsigner -verify -verbose filename.jar" is called, a separate section is printed out showing information of the signature and timestamp (if it exists) inside the signed JAR file, even if it is treated as unsigned for various reasons. If any algorithm or key used is considered weak, as specified in the Security property, jdk.jar.disabledAlgorithms, it will be labeled with "(weak)"
 OperaOpera 109.0 Build 5097.45
OperaOpera 109.0 Build 5097.45 PhotoshopAdobe Photoshop CC 2024 25.6
PhotoshopAdobe Photoshop CC 2024 25.6 PrivadoVPNPrivadoVPN 3.8.11
PrivadoVPNPrivadoVPN 3.8.11 ReiBootTenorshare ReiBoot iOS for Mac 9.4.4
ReiBootTenorshare ReiBoot iOS for Mac 9.4.4 Adobe AcrobatAdobe Acrobat Pro 2024.002.20687
Adobe AcrobatAdobe Acrobat Pro 2024.002.20687 OKXOKX - Buy Bitcoin or Ethereum
OKXOKX - Buy Bitcoin or Ethereum ParallelsParallels Desktop 19.3.0
ParallelsParallels Desktop 19.3.0 TradingViewTradingView - Track All Markets
TradingViewTradingView - Track All Markets CleanMyMacCleanMyMac X 4.15.3
CleanMyMacCleanMyMac X 4.15.3 4DDiG4DDiG Mac Data Recovery 3.4.2
4DDiG4DDiG Mac Data Recovery 3.4.2






Comments and User Reviews