-
Latest Version
Safari LATEST
-
Review by
-
Operating System
macOS 10.15 Catalina or later
-
User Rating
Click to vote -
Author / Product
-
Filename
Safari.dmg
Built-in privacy features are stronger than ever. It works with iCloud to let you browse seamlessly across all your devices. And it gives you great ways to find and share your favorites. Put it all together, and no other web browser offers such a rich web experience. Get the latest version of Safari for your Mac!
Longer battery life and faster performance
With a blazing-fast JavaScript engine and energy-saving technologies, Safari for macOS is a faster, more enjoyable way to explore the web.
Browse longer. Watch more
The browser is engineered specifically for Mac, so it takes advantage of the powerful technologies built into every one. And the app now offers native support for Netflix. So compared with Chrome and Firefox, you can browse for up to two hours longer and watch Netflix videos up to three hours long.
Defending your online privacy and security
Privacy and security aren’t just something you should hope for — they’re something you should expect. That’s why features to help protect your privacy and keep your Mac secure are built into the tool. For example, it’s the only browser to offer DuckDuckGo — a search engine that doesn’t track you — as a built-in option.
Surf seamlessly across all your devices
Not only does the program come on every Mac, but it also comes on every iPhone, iPad, and iPod touch, too. And thanks to iCloud, your passwords, bookmarks, history, tabs, and Reading List are always up to date no matter which device you're using.
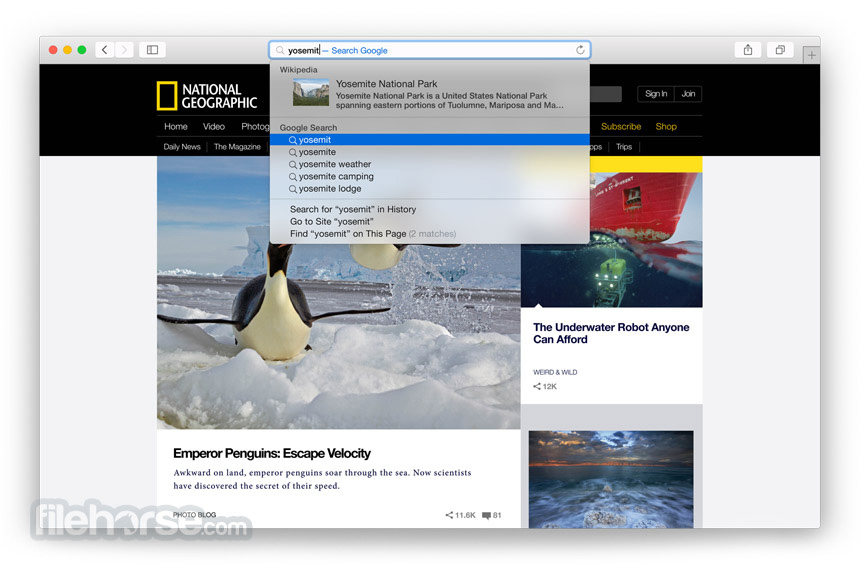
Spotlight suggestions
With Spotlight built into every Mac, you’re never far from the information you want. As you type in the Smart Search field, Spotlight suggestions display results from sources like Wikipedia, news sites, Maps, iTunes, movie listings, and more.
Share menu
Share anything you come across on the web without leaving the browser. Just click the Share button, then choose how you want to send it off. Use Mail, Messages, or AirDrop. Tweet or post to Facebook. And even add comments and locations. A single sign-on sets up sharing to Facebook and Twitter, so you only need to log in once. Download, Install or Update Safari for Mac!
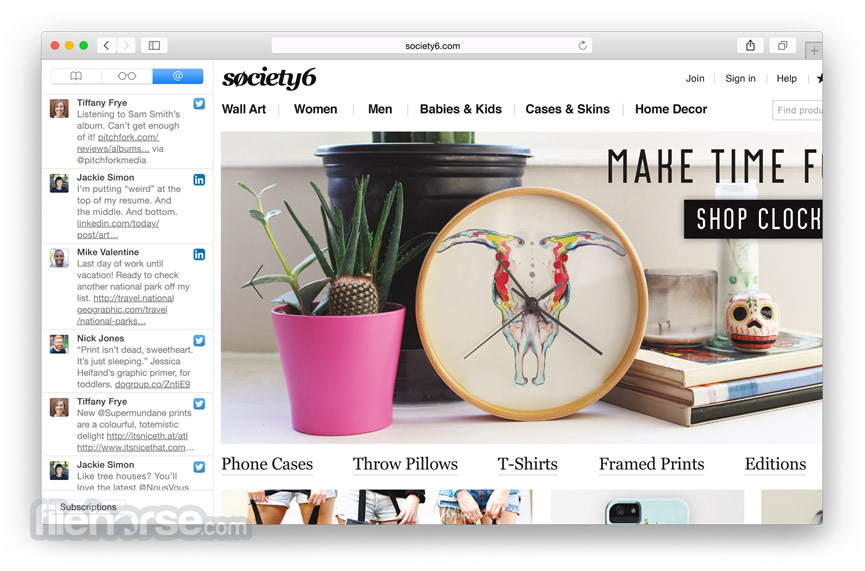
Shared Links
Shared Links is the best way to see what’s up on the web. When you’re in the mood to read something new, quirky, or cool, open Shared Links in the Safari Sidebar, where you can view links from people you follow on Twitter and LinkedIn. You can scroll seamlessly from one story to the next, no clicking required.
Reader
View news stories and other articles in a layout that’s optimized for easy reading. Reader lets you focus on the text without being distracted by ads and other items.
Developers
The tool is built on WebKit, the industry-leading open source rendering engine. It includes powerful built-in tools, like Web Inspector, that let developers create advanced web applications. And it continues to support technologies that enable innovation on the web.
Extensions
The browser Extensions are a great way to bring new features to the app. Customize your browsing experience by adding your favorite extensions.
Note: Requires 64-bit processor.
Also Available: Download Safari for Windows
-
Safari Screenshots
The images below have been resized. Click on them to view the screenshots in full size.
 OperaOpera 109.0 Build 5097.45
OperaOpera 109.0 Build 5097.45 PhotoshopAdobe Photoshop CC 2024 25.6
PhotoshopAdobe Photoshop CC 2024 25.6 PrivadoVPNPrivadoVPN 3.8.11
PrivadoVPNPrivadoVPN 3.8.11 ReiBootTenorshare ReiBoot iOS for Mac 9.4.4
ReiBootTenorshare ReiBoot iOS for Mac 9.4.4 Adobe AcrobatAdobe Acrobat Pro 2024.002.20687
Adobe AcrobatAdobe Acrobat Pro 2024.002.20687 OKXOKX - Buy Bitcoin or Ethereum
OKXOKX - Buy Bitcoin or Ethereum ParallelsParallels Desktop 19.3.0
ParallelsParallels Desktop 19.3.0 TradingViewTradingView - Track All Markets
TradingViewTradingView - Track All Markets CleanMyMacCleanMyMac X 4.15.1
CleanMyMacCleanMyMac X 4.15.1 4DDiG4DDiG Mac Data Recovery 3.4.2
4DDiG4DDiG Mac Data Recovery 3.4.2







Comments and User Reviews